5 Top Causes of Data Breaches - Data Breach Causes Explained
Data Breach Cyberattack Trends
What is a data breach? Data breach is a security incident where an unauthorized party accesses sensitive, protected, or …

Learn what went wrong in 20 of the largest data breaches ever recorded.
• Delayed disclosure made nearly every breach on this list worse. Yahoo revised its breach count from 1 billion to 3 billion a year later. Check if your data’s already out there before attackers find it first
• Marriott’s attackers sat inside Starwood’s network for four years undetected. Monitor for stolen credentials continuously, because the gap between breach and discovery is where the real damage happens
• Two companies on this list (National Public Data and Exactis) went bankrupt after their breaches. How you respond matters as much as the breach itself
• Weak or reused passwords were the common thread across most of these cases. Even old breaches from dead platforms like MySpace fueled credential stuffing attacks on other services years later
It’s not enough to secure your own infrastructure.
Attackers can exploit your vendors and partners to access your data too.
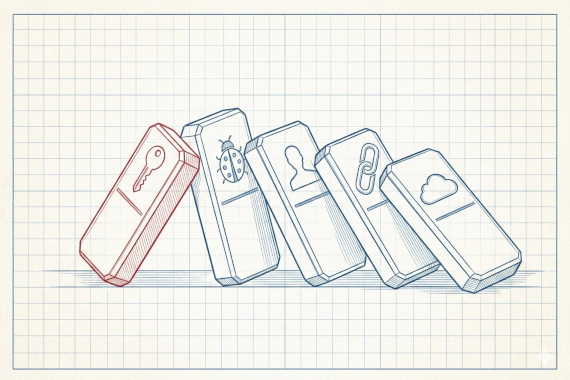
From unpatched vulnerabilities to stolen credentials, attackers steal data for financial gain and fraud.
Here are the 20 biggest data leak cases in recent history and what you can learn from each one.
Date: August 2013 Impact: 3 billion records
Yahoo holds the record for the largest data breach in history, and it’s not even close.
In October 2017, Yahoo (by then part of Oath Inc.) admitted that every single account that existed in 2013, all 3 billion of them, had been compromised. Their original 2016 disclosure had put the number at 1 billion. The real number was three times worse.
Attackers got away with names and email addresses. They also grabbed phone numbers, dates of birth, MD5-hashed passwords, and security questions with answers (some encrypted, some not).
The Department of Justice eventually charged two Russian FSB officers and two other attackers with the breach. The timing couldn’t have been worse for Yahoo. Verizon was in the middle of acquiring the company when the breach came to light, knocking $350 million off the sale price. Yahoo also paid out a $50 million settlement fund to affected users.
Date: December 2023 Impact: 2.9 billion records
National Public Data was a Florida-based data broker that ran employee background checks. In December 2023, their database of 2.9 billion records was stolen.
The database contained names and addresses for people in the US, UK, and Canada, plus Social Security numbers and phone numbers.
A member of the criminal group “USDoD” initially listed the database for sale at $3.5 million in April 2024. Four months later, a different USDoD member posted the entire thing for free on a hacker forum.
The parent company, Jerico Pictures, was buried under lawsuits and filed for bankruptcy.
You’ll see “data leak” and “data breach” used throughout this article. Here’s the difference.
Data leak is any incident where sensitive information gets exposed to unauthorized parties. It can happen through a deliberate attack or an accidental misconfiguration. “Data breach” is often used interchangeably, though a breach typically means an attacker broke through security controls, while a leak can also mean the data was left exposed unintentionally.
Date: January 2018 Impact: 1.1 billion records
India’s national ID system, Aadhaar, was breached in 2018. Over 1.1 billion residents had their names and addresses exposed. Photos and phone numbers were also part of the leak.
Tribune News Service reported that unauthorized access to the database was being sold through WhatsApp groups for 500 rupees (about $8 USD). That’s how cheap it was to buy access to the identity records of an entire country.
The Unique Identification Authority of India (UIDAI) first denied any breach happened. They later walked that back and added mandatory facial authentication and virtual ID numbers as extra safeguards. Indian officials maintained that core biometric data stayed secure.
Date: November 2019 Impact: 1.1 billion records
This one wasn’t a hack in the traditional sense. A developer working for a Chinese marketing company scraped 1.1 billion pieces of user data from Alibaba’s Taobao shopping platform over eight months, from November 2019 to July 2020.
He collected user IDs and mobile phone numbers, along with customer comments.
Alibaba didn’t catch it until July 2020. Both the developer and his employer were convicted. They each got three years in prison and a fine of 450,000 Yuan (about $70,260 USD).
Date: June 2021 Impact: 700 million users
An attacker scraped data from 700 million LinkedIn profiles, roughly 92% of the platform’s users at the time, and posted a 1 million record sample on a dark web forum with the full dataset for sale.
The scrape pulled email addresses and full names. It also included phone numbers, physical addresses, geolocation records, and work history.
LinkedIn was quick to point out that no private account data was compromised, since the attacker exploited their API to pull publicly visible profile data. That’s technically true, but misses the point. A consolidated dataset of 700 million profiles is extremely useful for social engineering and targeted phishing.
Date: March 2020 Impact: 538 million users
Sina Weibo, China’s equivalent of Twitter, lost data on 538 million users. The attacker listed the database on a dark web market for just 1,799 Chinese Yuan (about $250 USD).
Real names and usernames were exposed for 172 million users. Phone numbers and location data were in the dataset too. No passwords were included, which probably explains the bargain-bin price. Still, the phone numbers alone could be used for account takeover attempts through SMS verification.
Date: April 2019 Impact: 533 million users
In April 2019, attackers exploited a vulnerability in Facebook’s contact sync feature, specifically the phone number lookup tool, to scrape data from 533 million users across 106 countries.
The scrape captured Facebook IDs and full names, plus phone numbers. Locations and birthdates came with them, along with email addresses.
The breach got a second life in 2021 when the complete dataset was posted for free on a hacker forum. At that point, anyone could download it.
Date: November 2018 Impact: 500 million guests
The largest breach in hospitality history started in 2014 inside Starwood’s reservation system, two years before Marriott even acquired the company. Nobody caught it until September 2018.
Four years of access gave the attackers plenty of time. They got their hands on 5.25 million unencrypted passport numbers and 8.6 million encrypted credit card credentials, on top of the usual personal details for 500 million guests.
Western intelligence agencies attributed the attack to Chinese state-sponsored attackers.
Marriott faced class-action lawsuits and an £18.4 million fine from the UK’s Information Commissioner’s Office. They also had to reimburse fraud victims for new passports. Total breach-related costs exceeded $100 million.
Date: 2014 Impact: 500 million accounts
Yes, Yahoo is on this list twice.
In September 2016, Yahoo disclosed a separate breach affecting 500 million accounts. At the time, it was the largest cybersecurity breach ever reported (before their own 2013 breach turned out to be six times bigger).
According to the DOJ indictment, a Russian national named Alexey Belan copied a backup of Yahoo’s user account database. Most passwords were hashed with bcrypt, which is hard to crack, but a portion used MD5, which is not.
Belan and several others used the stolen data to search victim emails for gift voucher codes and manipulate search rankings for businesses they had interests in. They also ran credential-stuffing attacks against Gmail and other platforms.
Date: November 2016 Impact: 412 million accounts
This breach hit multiple Friend Finder Network properties, including Adult Friend Finder and Cams.com. Penthouse.com and Stripshow.com were affected too, along with iCams.com. The data went back 20 years and covered 412 million accounts.
Usernames and passwords (stored in either plaintext or SHA1) were exposed, along with email addresses and IP addresses. Last visit dates and browser fingerprints leaked too. Given the nature of these sites, the data also revealed users’ sexual preferences, opening the door to blackmail.
A month before the breach, a security researcher had publicly disclosed a local file inclusion vulnerability on the site. That may have been the way in.
Making things worse, the company had kept data from 15 million deleted accounts, all of which was exposed too. This came just over a year after a previous breach in 2015 that leaked 3.5 million accounts.
Several of the breaches on this list led to credential stuffing attacks. Here’s what that means.
Credential stuffing is when attackers take stolen username and password pairs from one breach and automatically test them against other websites. It works because people reuse passwords. A single leaked password from MySpace or LinkedIn can unlock a victim’s email or corporate accounts if they used the same password across services.
Date: May 2016 Impact: 360 million accounts
By 2016, nobody was really using MySpace anymore. But the breach that surfaced in May 2016 had actually happened back in June 2013, when the platform still had a massive user base.
An attacker known as “Peace_of_mind” put 360 million accounts up for sale on the dark web. The dataset included usernames and email addresses, plus SHA1-hashed passwords. SHA1 is weak enough that cracking those passwords was straightforward.
The real damage came from password reuse. Many users had abandoned their MySpace accounts years ago but were still using the same passwords elsewhere. Attackers exploited this through credential stuffing to break into accounts on other platforms.
Date: June 2018 Impact: 340 million records
Exactis was a Florida-based marketing and data aggregation firm. Security researcher Vinny Troia found a 2-terabyte database sitting on a publicly accessible server.
What set this breach apart was the depth of the data. Each record contained up to 400 data points, including phone numbers and home addresses. Interests and personal habits were logged too. Some records even included details about people’s children. This wasn’t just contact info. It was a detailed behavioral profile.
The lawsuits piled up. Exactis filed for bankruptcy in 2019. When your entire business is managing other people’s data, losing it all tends to be fatal.
Date: January 2023 Impact: 235 million users
A vulnerability in Twitter’s API let attackers match email addresses and phone numbers to accounts, even when users had hidden those fields in their privacy settings. Multiple attackers exploited the bug between June 2021 and January 2022.
The resulting database of 235 million users (email addresses, names, usernames, follower counts, creation dates) was initially listed for $30,000. A month later, someone posted the full 59 GB archive for free on BreachForums.
High-profile accounts caught up in the leak included Donald Trump Jr and Mark Cuban.
Date: October 2015 Impact: 235 million accounts
NetEase runs two of China’s biggest email services, 163.com and 126.com. In October 2015, 235 million accounts from those services were leaked.
Email addresses and usernames were exposed, along with passwords. Many were stored in plaintext or with weak hashing. In China’s digital ecosystem, email accounts are often tied to gaming platforms and payment services, which made the stolen credentials useful far beyond email access.
Date: October 2013 Impact: 200 million records
A Vietnamese national named Hieu Minh Ngo posed as a private investigator to get a subscription to Court Ventures’ consumer database. Through that subscription, he accessed names and addresses for 200 million people. He got Social Security numbers and bank account details too.
He then sold the data to identity thieves. Over 1,300 customers bought stolen personal information through his service.
The alarming part: Ngo kept his access for 18 months after Experian acquired Court Ventures. Nobody thought to audit who had database access during the acquisition.
Ngo was arrested in 2013 after U.S. Secret Service agents lured him to Guam. He was sentenced to 13 years in prison. The breach triggered congressional inquiries and class-action lawsuits.
Date: June 2012 Impact: 165 million users
LinkedIn’s first appearance on this list. In June 2012, 6.5 million password hashes showed up on a Russian hacker forum.
The full scale only became clear later when “Peace_of_mind” (the same attacker behind the MySpace leak) put 165 million LinkedIn accounts up for sale for five bitcoins, about $2,000 at the time.
The passwords were stored as unsalted SHA-1 hashes, making them trivially easy to crack. Even by 2012 standards, SHA-1 was considered inadequate. LinkedIn settled the resulting class-action suit for $1.25 million in 2015.
Date: December 2018 Impact: 162 million users
Dubsmash, a video sharing app, was breached in December 2018 but didn’t disclose it until February 2019, when the stolen data turned up for sale on the dark web.
Usernames and email addresses were listed for around $1,000 in Bitcoin, along with MD5-hashed passwords. The data later got bundled with 15 other breached sites into a collection of 620 million accounts. Bundling multiple breaches together drives up the price and makes the combined dataset far more useful for credential-stuffing attacks.
Date: October 2013 Impact: 153 million users
Security researcher Brian Krebs found a 40 GB file containing Adobe source code and a 3.8 GB file called “users.sql.tar.gz” with credentials for 153 million users. Both files were sitting on the same server that attackers had used to breach LexisNexis and Dun & Bradstreet.
The stolen credentials included email addresses and encrypted passwords. Plaintext password hints were exposed too, and some records contained credit card details. Adobe settled for $1.1 million. It’s now a go-to example of what bad encryption practices get you.
Date: September 2017 Impact: 147.9 million consumers
Roughly half the US population had their data exposed because Equifax didn’t patch a known vulnerability in Apache Struts (CVE-2017-5638). Attackers exploited it between May and July 2017 and walked away with Social Security numbers and birth dates. They also grabbed addresses and about 209,000 credit card numbers.
Equifax’s response made everything worse. They waited six weeks to disclose. The website they built for consumers to check their exposure originally included arbitration clauses that would waive your right to sue. Their official Twitter account accidentally linked to a phishing site.
The CEO, CIO, and CSO resigned. Equifax paid $700 million to settle federal and state investigations.
Date: May 2014 Impact: 145 million users
Attackers compromised eBay employee credentials and used them to sit inside eBay’s corporate network for 229 days. This is a textbook example of why credential monitoring matters.
eBay lost names and encrypted passwords (bcrypt, which is hard to crack). Email addresses and physical addresses were also taken, along with phone numbers. Financial information was stored separately and wasn’t compromised.
229 days of undetected access. Even with bcrypt protecting the passwords, that’s more than enough time to exfiltrate everything else.
The pattern across these 20 breaches is consistent: stolen or weak credentials got attackers in, and slow detection let them stay. Two companies on this list went bankrupt. Others paid hundreds of millions in fines and settlements.
The gap between when a breach happens and when you find out is where the real damage piles up. Start with a free dark web scan to check if your credentials are already exposed, or book a demo to see how Breachsense catches stolen credentials before attackers use them.
Yahoo’s 2013 breach holds the record at 3 billion accounts. The company initially reported 1 billion affected accounts in 2016 before revising the number upward in 2017. The DOJ charged two Russian FSB officers with the attack.
Many of the largest breaches went undetected for months or years. Marriott’s breach ran for four years before discovery. eBay’s attackers had network access for 229 days. Faster detection through credential monitoring directly reduces the damage.
It depends on who gets breached. Email addresses and passwords are the most common. But breaches of data brokers like National Public Data and Exactis also exposed Social Security numbers and detailed personal profiles.
Yes. National Public Data filed for bankruptcy after its 2.9 billion record breach. Exactis went bankrupt in 2019 after exposing 340 million records. Companies whose primary business is managing data are most vulnerable to this outcome.
Credential stuffing is when attackers take stolen passwords from one breach and test them against other websites. It works because people reuse passwords. Breaches from MySpace and LinkedIn fueled credential stuffing attacks on completely unrelated platforms.
Costs vary widely. Yahoo’s breach knocked $350 million off its sale price to Verizon. Equifax paid $700 million in settlements. Marriott spent over $100 million. Beyond fines, companies lose customers and face executive turnover.
Data Breach Cyberattack Trends
What is a data breach? Data breach is a security incident where an unauthorized party accesses sensitive, protected, or …

What is data breach compliance? You’ll see this term in vendor contracts and regulatory filings. Here’s what it actually …