
6-Phase Ransomware Response Plan: Detect and Recover Fast
Why Do You Need a Ransomware Response Plan? A ransomware attack at 2am isn’t the time to figure out who makes decisions, …

Learn what dark web monitoring is and how to choose the right service for your team.
• Dark web monitoring scans criminal sources for your leaked credentials and data. It gives you time to reset passwords before attackers use them.
• Source coverage separates good monitoring from bad. Services that only check old breach compilations miss stealer logs, where fresh credentials appear within hours of infection.
• Detection speed only matters if you act on alerts. Build response workflows first, then buy a monitoring service.
• You’ll often detect vendor breaches through monitoring before the vendor tells you. That early warning is one of the biggest practical benefits.
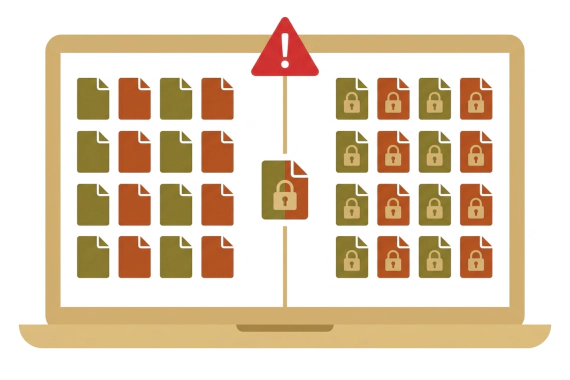
Stolen credentials are the most common way attackers get in. Most ransomware victims had their credentials exposed on the dark web before the attack even happened.
Credentials leak through paths you don’t control. Vendors get hacked. Employees reuse passwords. Infostealer malware grabs saved passwords from browsers, and criminals sell them the same day.
When monitoring catches a leaked password, you reset it. The attacker loses access before they can use it.
This guide covers how dark web monitoring works, what features matter, and how to pick the right vendor.
Your credentials could be for sale right now. You’d never know unless you’re actively looking.
Dark web monitoring is the practice of scanning criminal forums and infostealer channels for your exposed credentials and data. When your information appears in these sources, you’re notified so you can reset passwords and revoke sessions before anyone exploits them.
The dark web isn’t indexed by Google. Accessing it requires specialized tools like the Tor browser. Criminals use it because anonymity makes them nearly impossible to track.
Your data ends up there through paths you don’t control. A service your team uses gets hacked and your credentials leak with it. Infostealer malware harvests passwords directly from employee browsers. The 2025 Verizon DBIR found that 54% of ransomware victims had credentials exposed in infostealer data before the attack.
Dark web monitoring services let security teams see what’s happening in these underground channels. When your credentials show up, you can respond before they get exploited.
Dark web monitoring platforms combine automated collection with human intelligence to find leaked data targeting your domains. For details on how Breachsense specifically monitors dark web sources, see our methodology page.
Getting access is the hard part. Private forums vet members. Criminal channels come and go. That’s where fresh credentials appear first.
Stealer logs are collections of credentials harvested by infostealer malware from infected devices. Each log contains usernames and passwords stolen from a victim’s browser. Session tokens are often included too, which let attackers bypass MFA entirely. Criminals sell these logs in bulk on dark web marketplaces.
Stealer logs deserve special attention. Unlike breach data that gets leaked months after the initial compromise, these logs appear within hours of infection. Monitoring these channels gives you the fastest detection possible.
Raw dark web data is messy. Credentials come in various formats. Some dumps are fake or recycled from old breaches.
Dark web monitoring software normalizes this data and matches it against your monitored assets. When your corporate domain appears in a credential dump, the service flags it. The best dark web monitoring platforms also show you the source type and when the data first appeared.
When matches are found, you get alerted. Some services only send email notifications, but API integrations are far more useful. They push alerts directly to your SIEM or SOAR platform so you can correlate them with your other logs and threat intel.
Alert quality matters as much as speed. You need enough context to prioritize your response. Credentials from a recent stealer log are more urgent than a years-old combo list.
Finding exposed data is only valuable if you act on it. When credentials leak, reset them immediately. When stolen sessions appear, invalidate them.
Attackers often have the same data you’re seeing. How fast you respond decides whether you fix the problem or suffer a breach.
Not all dark web monitoring services are equal. Here’s how to evaluate what actually matters.
This is the most important factor. Most dark web security monitoring services now cover breach compilations and infostealer data. The real gap is whether they also extract text from leaked ransomware files and index unsecured databases. That’s where a lot of sensitive data hides.
Each source type serves a different purpose:
The freshness hierarchy matters. Infostealer data provides the earliest warning since credentials appear almost immediately after infection. Private forum data comes next. Public paste sites typically show data that’s weeks or months old.
Ask vendors specifically about their source coverage. Vague claims often hide limited actual access. Request specifics: how many criminal channels do they monitor? Do they have access to Russian-language forums?
How quickly can the dark web monitoring tool detect new exposures? Monitoring active criminal channels requires near-real-time collection.
Your response window depends on detection speed. If new exposures appear quickly but your monitoring service only checks weekly, attackers have days to exploit them before you know.
Different sources have different timing expectations:
Ask vendors about their collection frequency for each source type. A service that checks channels once per day will miss posts that get deleted quickly.
Raw alerts aren’t enough. You need context to know what to act on first. When was this data first seen? Where did it come from? Is it current or recycled?
Good dark web credential monitoring includes:
Without this context, your team wastes time chasing exposures that no longer matter.
Your monitoring only matters if it connects to your security operations. API access lets you automate workflows. SIEM integration puts alerts alongside your other security data.
Manual processes don’t scale. If checking alerts requires logging into a separate dashboard, alerts will get delayed or missed. Your security team already has too many tools to check.
Credential monitoring tools that connect to your existing security stack deliver faster outcomes than standalone dashboards. Look for services that support webhooks and API-driven response so compromised credentials trigger automatic password resets.
Here are the most common alerts you’ll see and what they mean:
Employee credentials in stealer logs. An employee’s device gets infected with infostealer malware. Within hours, their saved passwords appear for sale. This is the most urgent alert type because the credentials are fresh and likely still valid.
Corporate domains in breach dumps. A vendor or service your team uses gets breached. Employee credentials from that service appear in a dump. These often surface before the vendor publicly discloses the breach.
Session tokens for sale. Attackers don’t always need passwords. Stolen session cookies let them skip multi-factor authentication and log directly into active sessions. These alerts require immediate invalidation.
Sensitive documents on ransomware leak sites. Ransomware gangs publish stolen files when victims don’t pay. If your company’s documents appear on a leak site, you need to assess what was exposed and notify affected parties.
Executive or VIP credential exposure. C-suite credentials get targeted specifically. Alerts on executive accounts should trigger immediate response regardless of the source.
When you get an alert, your first step is checking the context. Fresh infostealer data means change those passwords now. Old breach data might just need verification that credentials have already been rotated.
Choosing a vendor means cutting through marketing claims to assess actual capabilities. Most vendors claim broad coverage. Few can prove it.
Ask for specific examples of source types monitored. Request sample data from different categories. A vendor who can’t show you ransomware file extraction or unsecured database coverage is probably just repackaging the same data everyone else has.
Questions to ask during evaluation:
Look for evidence of active collection, not just data sharing agreements. Direct access to sources provides faster detection than receiving data second-hand.
Ask how often they collect from different source types. Request case studies showing detection-to-alert timelines. If you have credentials you know were leaked in a recent breach, check whether the vendor’s platform already shows them.
Services that tout “real-time” monitoring should demonstrate what that means operationally. Daily scans aren’t real-time. Neither are weekly batch imports from data partners.
Not all dark web data is useful. Old compilations get recycled endlessly. Fake dumps exist to sell subscriptions. You need a vendor whose data you can actually trust.
Red flags for poor data quality:
Ask how the vendor filters out recycled or fake data. Good services deduplicate against known breaches and track source reputation.
Test integrations during evaluation, not after purchase. A vendor demo isn’t the same as your team actually connecting the service to your SIEM.
Key integration questions:
Dark web monitoring gives you early warning when credentials leak. The value comes from acting on that warning. Reset the password before the attacker logs in. Invalidate the session token before it gets used.
Pick a vendor with strong source coverage. Stealer logs and private forums are baseline now. The real differentiator is whether they extract data from ransomware leak files and unsecured databases. Make sure alerts flow into your existing security tools so your team actually sees them. For vendor comparisons, see our guides to the best dark web monitoring services and best dark web monitoring tools.
Detect your leaked credentials before attackers do. Book a demo to see how Breachsense monitors stealer logs and hacker forums. Or run a free dark web scan to check your exposure now.
Dark web monitoring continuously scans criminal marketplaces and private forums for your exposed credentials. It covers infostealer data, breach dumps, and ransomware leak sites. You get alerted when your data appears so you can act before anyone exploits it.
Monitoring services collect data from dark web sources including infostealer data and private forums. They match credentials against your monitored domains and alert you when matches come back. Good services tell you where the data came from and how fresh it is.
Breach notification services tell you when a company publicly reports a breach. Dark web monitoring scans criminal sources to find your data directly. You’ll often find exposures on the dark web weeks before companies disclose breaches.
A dark web monitoring alert means your credentials or data appeared in a criminal source. It could be a stealer log from malware on an employee’s device or a leaked file from a vendor breach. Check the alert context to decide what to do first.
It can prevent credential-based breaches. When you find leaked passwords early, you reset them before attackers log in. It can’t prevent the initial breach that exposed the data, but it closes the window attackers have to exploit stolen credentials.
Source coverage matters most. The service should monitor stealer logs and ransomware leak sites, not just third-party breaches and combo lists. Look for real-time alerting with data freshness context, plus API integration so alerts flow into your existing security tools.
Speed depends on the service and source type. Good infostealer monitoring can detect credentials the same day they’re stolen. Breach data takes longer because criminals don’t always leak immediately. Ask vendors how often they collect from each source type.
Compare it to the cost of a breach. The 2025 IBM Cost of a Data Breach Report puts the average breach at $4.88 million. Preventing one account takeover can justify years of monitoring costs.

Why Do You Need a Ransomware Response Plan? A ransomware attack at 2am isn’t the time to figure out who makes decisions, …
Ransomware Detection Threat Intelligence Dark Web Monitoring Credential Monitoring Cybersecurity
What Is Ransomware Detection? Most companies discover ransomware when files start disappearing or ransom notes appear. …