
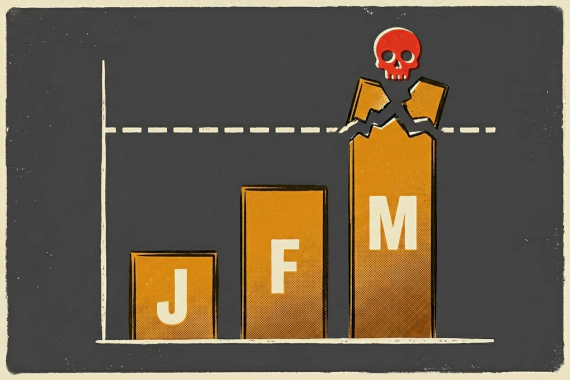
April 2026 Ransomware Report: 772 Victims, 70 Groups
Ransomware Threat Intelligence Dark Web Monitoring Cybersecurity Trends
April 2026 ransomware numbers at a glance After March’s spike, April pulled back slightly. Here’s what changed. …

Ransomware Threat Intelligence Dark Web Monitoring Cybersecurity Trends
April 2026 ransomware numbers at a glance After March’s spike, April pulled back slightly. Here’s what changed. …

Threat Intelligence Dark Web Monitoring Infostealer Malware Ransomware Identity Security
What 2025 actually looked like Breachsense has indexed 90+ billion identity records across third-party breaches, …
Indicators of Compromise IOC Threat Intelligence Dark Web Monitoring Cybersecurity Breach Detection
IOCs work. But they work after the fact. By the time you find a malicious file hash or C2 beacon, attackers have already …

Insider Threat Threat Intelligence Data Breach Prevention Security Operations
What Are Insider Threat Indicators? Security teams spend billions on perimeter defenses like firewalls and EDR. But 60% …

Threat Intelligence Dark Web Monitoring Security Tools
What Is Cyber Threat Monitoring? Security teams can’t protect what they can’t see. Cyber threat monitoring shows you …
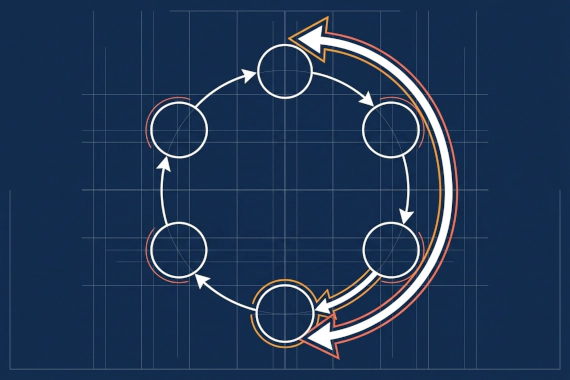
Threat Intelligence Cybersecurity CTI Security Operations
What Is the Threat Intelligence Lifecycle? The threat intelligence lifecycle is a six-phase process that turns raw …
Ransomware Threat Intelligence Dark Web Monitoring Cybersecurity Trends Infostealer
What Are the Current Ransomware Trends? Ransomware volume continues to climb. The Verizon 2025 DBIR found ransomware …
Threat Intelligence Cybersecurity Strategy SOC Operations
What Is Cyber Threat Intelligence? There’s a difference between having threat feeds and having threat intelligence. Most …
Ransomware Cyberattack Trends Threat Intelligence Dark Web
What Is Ransomware? Ransomware is malicious software that encrypts files on infected systems and demands payment for the …
Ransomware Detection Threat Intelligence Dark Web Monitoring Credential Monitoring Cybersecurity
What Is Ransomware Detection? Most companies discover ransomware when files start disappearing or ransom notes appear. …
Ransomware Threat Intelligence Dark Web Monitoring Cybersecurity Trends
March 2026 ransomware numbers at a glance March was the busiest month of 2026 so far. Here’s what it means for you. …

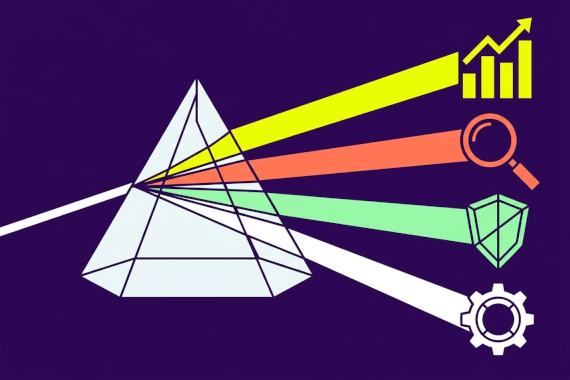
Threat Intelligence Cybersecurity CTI Security Operations
What Do We Mean by Levels of Threat Intelligence? Cyber threat intelligence (CTI) isn’t one thing. It’s three layers …

Insider Threat Data Breach Prevention Security Operations Threat Intelligence
What Is an Insider Threat? Most security tools focus on keeping attackers out. Firewalls, intrusion detection, perimeter …

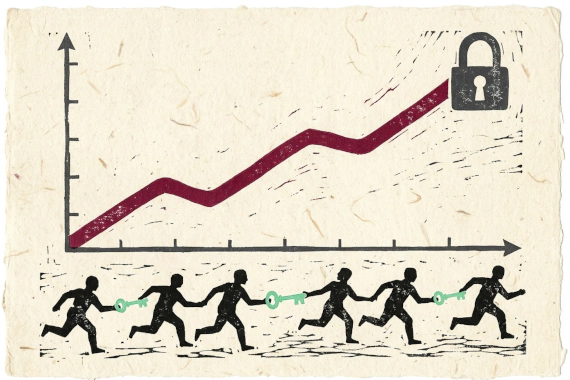
Threat Intelligence Cybersecurity Enterprise Security
Why Do You Need a Threat Intelligence Platform? Traditional firewalls can’t protect against stolen passwords. VPNs don’t …

Digital Risk Protection DRP Security Dark Web Monitoring Threat Intelligence Cybersecurity
What is Digital Risk Protection? Most security teams watch their internal networks. DRP platforms watch everywhere else. …

Email Security Threat Intelligence
What Are Email Security Threats? Your email is the front door to your organization. It’s the top initial access vector …

Digital Risk Monitoring Digital Risk Management Third Party Risk Threat Intelligence Dark Web Monitoring External Threats
Most companies have some external monitoring, but it’s not enough. Attacks start on dark web marketplaces where your …

Dark Web Threat Intelligence OSINT Breach Monitoring
What Are Dark Web Sites? The internet has three layers. Most people only ever see one. Dark web sites are websites …

Dark Web Monitoring Threat Intelligence
What Is Dark Web Monitoring? Your credentials could be for sale right now. You’d never know unless you’re actively …

Threat Intelligence Dark Web Monitoring
What Is Cyber Threat Intelligence Software? You can’t monitor every dark web forum and criminal channel yourself. CTI …

Ransomware Monitoring Dark Web Monitoring Threat Intelligence Credential Monitoring
What Is Ransomware Monitoring? You’ll see “ransomware monitoring” used loosely across vendor marketing. Here’s what it …

Dark Web Monitoring Recorded Future Threat Intelligence Compromised Credentials Credential Monitoring
How Does Recorded Future Handle Dark Web Monitoring? Recorded Future is a threat intelligence platform that includes …
Dark Web Monitoring ZeroFox Digital Risk Protection Compromised Credentials Threat Intelligence
How Does ZeroFox Handle Dark Web Monitoring? ZeroFox is a digital risk protection platform that includes dark web …
Dark Web Monitoring Flare Threat Intelligence Credential Monitoring Threat Exposure Management
What Does Flare Do Well? Flare built their platform around Threat Exposure Management. They combine dark web monitoring …
Dark Web Monitoring Group-IB Threat Intelligence Credential Monitoring Digital Risk Protection
What Does Group-IB Do Well? Group-IB is a cybersecurity company that sells a suite of products under their Unified Risk …

Credential Monitoring Dark Web Monitoring Compromised Credentials Threat Intelligence Infostealer Detection
What Does Credential Monitoring Actually Cover? “Credential monitoring” means different things depending on the vendor. …
Dark Web Monitoring DarkOwl Threat Intelligence Credential Monitoring Dark Web Intelligence
What Does DarkOwl Do Well? DarkOwl is a darknet data platform. They collect content from across the dark web and make it …
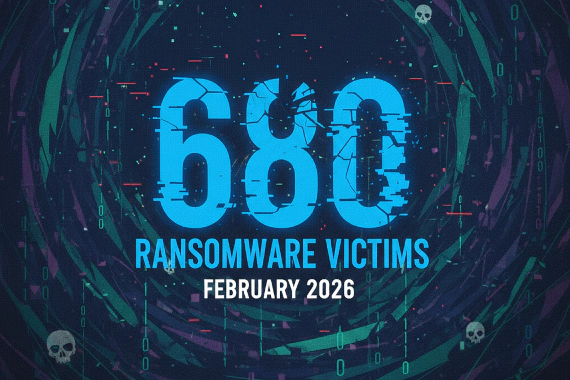
Ransomware Threat Intelligence Dark Web Monitoring Cybersecurity Trends
February 2026 ransomware numbers at a glance You’ll see “leak site” throughout this report. Here’s what that means. …
Dark Web Monitoring Compromised Credentials Group-IB Threat Intelligence Credential Monitoring
What Does Group-IB Do? Group-IB is a cybersecurity company that sells a suite of products under their Unified Risk …

Dark Web Monitoring Threat Intelligence Cybersecurity Glossary Breach Detection
What Does This Page Cover? Security teams deal with dozens of specialized terms when evaluating dark web monitoring …

Digital Risk Protection Dark Web Monitoring Compromised Credentials Threat Intelligence Credential Monitoring
What Does Digital Risk Protection Actually Cover? Vendors use “digital risk protection” loosely. Gartner and Forrester …

Dark Web Monitoring Compromised Credentials Flare Threat Intelligence Credential Monitoring
What Does Flare Do? Flare is a threat exposure management platform. They monitor dark web sources and clear web …
Ransomware Threat Intelligence Dark Web Monitoring Cybersecurity Trends
January 2026 ransomware numbers at a glance You’ll see “leak site” throughout this report. Here’s what that means. …

Dark Web Monitoring Compromised Credentials SpyCloud Threat Intelligence Credential Monitoring
What Does SpyCloud Do Well? SpyCloud’s dark web monitoring focuses on extracting stolen credentials from third-party …
Data Breaches Ransomware Breach Tracking Threat Intelligence
What Does the Breach Tracker Show? The Breachsense breach tracker is a public feed of ransomware attacks and extortion …

Dark Web Monitoring Compromised Credentials DarkOwl Threat Intelligence Credential Monitoring
What Does DarkOwl Do? DarkOwl is a darknet data platform. They collect content from across the dark web and make it …
Dark Web Monitoring Threat Intelligence Credential Monitoring Security Research
What Is a Dark Web Market? When your credentials get stolen, they often end up for sale on a dark web market within …

Digital Risk Protection Threat Intelligence Dark Web Monitoring Cybersecurity Platforms Security Tools
What Are the Best Digital Risk Protection Platforms? Platform Best For Key Strength Breachsense Security teams, …
Insider Threat Security Tools UEBA Data Loss Prevention Threat Intelligence
Which Are the Top 10 Insider Threat Detection Tools? Insider threat detection software falls into four categories: UEBA …

Dark Web Monitoring Threat Intelligence
What Is Dark Web Threat Intelligence? Your employees’ credentials are probably for sale right now. The question is …

Dark Web Monitoring Threat Intelligence Cybersecurity Data Breach Detection
Which Dark Web Monitoring Services Made the List? Service Best For Key Strength Breachsense Security teams, MSPs, …

Ransomware Threat Intelligence Dark Web Monitoring Cybersecurity Trends
2025 ransomware numbers at a glance You’ll see “leak site” throughout this report. Here’s what that means. Breachsense …
Threat Intelligence Educational Content
What Is the Difference Between the Deep Web and Dark Web? The internet has three layers. Each one works differently and …

Threat Intelligence Security Tools SOC Operations
Threat intelligence feeds are the foundation of automated threat detection. They provide the indicators your security …

Dark Web Monitoring Threat Intelligence SocRadar Digital Risk Protection Credential Monitoring
What Does SocRadar Do? SocRadar markets itself as an “Extended Threat Intelligence” platform. That’s their branding for …
Data Breach Threat Intelligence
What Is A Password Combo List? Combo List: A file containing username and password pairs collected from data breaches …
Threat Intelligence Recorded Future Dark Web Monitoring Compromised Credentials Credential Monitoring
What Does Recorded Future Do? Recorded Future is an enterprise threat intelligence platform providing broad coverage …

Dark Web Monitoring Compromised Credentials SpyCloud Threat Intelligence Credential Monitoring
What Does SpyCloud Do? SpyCloud is an enterprise-focused platform that detects stolen credentials to prevent account …
Dark Web Monitoring Threat Intelligence Security Tools OSINT
What Is a Dark Web Search Engine? The dark web (sometimes called the black web or darknet) operates on a completely …

Data Breach Detection Dark Web Monitoring Credential Monitoring Cybersecurity Tools Threat Intelligence
What Are Data Breach Detection Tools? Most security tools watch your internal network. Breach detection tools watch …

Threat Intelligence Dark Web Monitoring Security Tools CTI
What Are Cyber Threat Intelligence Tools? Cyber threat intelligence tools give your security team information about …
Privacy Threat Intelligence Security Awareness
What Is Doxing? Someone posts your home address on a forum. Your phone starts ringing with threatening calls. Strangers …

Malware Threat Intelligence Credential Security
What Is a Keylogger? A keylogger does exactly what its name suggests. It logs your keystrokes. Keylogger is malware …
Brand Protection Threat Intelligence Phishing
Brand monitoring is the practice of tracking your company’s name and digital assets across the internet to detect …
Threat Intelligence Data Breach Credential Security
Breach intelligence is a specialized form of threat intelligence focused on collecting and analyzing information about …
Executive Protection Threat Intelligence BEC
Digital executive protection is a specialized security discipline focused on protecting high-profile individuals from …
Social Engineering Phishing Threat Intelligence
Pretexting is a social engineering technique where attackers create fabricated scenarios to manipulate victims into …
Malware Infostealers Threat Intelligence
Spyware is malicious software designed to secretly monitor and collect information from infected devices without the …
Stealer Logs Infostealer Credential Theft Dark Web Threat Intelligence
Stealer logs are packages of stolen data harvested by infostealer malware from infected devices. Each log contains …
Threat Intelligence Cybercrime Security Operations
Threat actors are individuals or groups that conduct malicious cyber activities against organizations, governments, or …
Vulnerability Management Threat Intelligence Security Operations
Vulnerability intelligence is the collection and analysis of information about software vulnerabilities. It goes beyond …

Zero-Day Exploits Vulnerability Management Threat Intelligence Cybersecurity Enterprise Security
What Is a Zero-Day Exploit? A zero-day exploit takes advantage of a software vulnerability that nobody knows about yet. …

Threat Intelligence OSINT Dark Web Security Operations
What Is Open Source Intelligence? Open source intelligence (OSINT) is the collection and analysis of publicly available …

Dark Web Monitoring Threat Intelligence Credential Monitoring
What Is Deep Web Monitoring? Most security discussions focus on the dark web. But threats often appear elsewhere first. …

What Are the Biggest Malware Trends Right Now? The malware landscape has fundamentally shifted. Traditional malware that …
Threat Intelligence Cybersecurity External Threat Intelligence CTI
What is External Threat Intelligence? External threat intelligence is threat data collected from outside your …

Threat Intelligence Educational Content
Why the Iceberg Metaphor is Wrong The iceberg model suggests a sinister hierarchy, implying that things get …

Cyberattack Trends Threat Intelligence
What are External Threats? External threats are cybersecurity risks originating from outside an organization that …