
How To Prevent Business Email Compromise (BEC) Scams
What Is Business Email Compromise? It goes by several names, but they all describe the same scam. Business email …

What Is Business Email Compromise? It goes by several names, but they all describe the same scam. Business email …

Third-Party Risk Best Practices
Why Are Third-Party Breaches So Hard to Prevent? You can lock down your own systems. You can train your own employees. …

Insider Threat Data Security Best Practices
What Is Employee Data Theft? The term covers more than you might think. It’s not just a disgruntled employee walking out …
Data Theft Prevention Data Security Best Practices
What Is Data Theft Prevention? Data theft is the unauthorized taking of sensitive information for financial gain or …

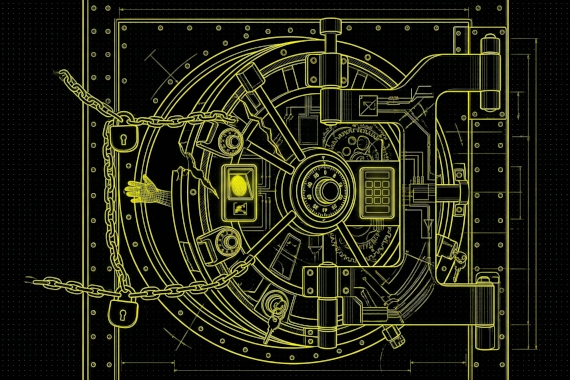
What Is Data Breach Protection? There’s no single product you can buy that stops breaches. Protection is a stack of …

Data Security Best Practices Best Practices
What Are the Most Important Data Security Best Practices? Not all security practices deliver equal value. Some save …

Data Leak Prevention Data Security Best Practices
What Is Data Leakage Prevention? Your sensitive data could be leaking right now through a misconfigured cloud bucket, a …

Dark Web Monitoring Best Practices
What Is Dark Web Monitoring for Business? Most security teams understand dark web monitoring in theory. The execution is …

Initial Response (First 24 Hours) During the first 24 hours after identifying a breach, security teams need to identify …

What is a data breach? A data breach occurs when sensitive information is accessed by unauthorized individuals. There …